A security algorithm co-authored by NXP Semiconductors has been selected by the US Department of Commerce's National Institute of Standards and Technology (NIST) as part of the Post-Quantum Cryptography (PQC) global standard to protect quantum computers from attacks. Cryptographic the CRYSTALS-Kyber lattice-based algorithm, presented by NXP in collaboration with IBM, Arm and academic partners, has been selected as the post-quantum public key standard.
The CRYSTALs-Kyber algorithm is one of the first four encryption algorithms selected by NIST after six years of work to develop encryption methods to protect against threats from quantum computers. The other three algorithms are CRYSTALS Dilithium, FALCON and SPHINCS+. These algorithms are based on structured lattices and hash functions.
NIST is considering four additional algorithms, including the classic McEliece, co-authored by NXP, which is advancing to the fourth and final round for further analysis.
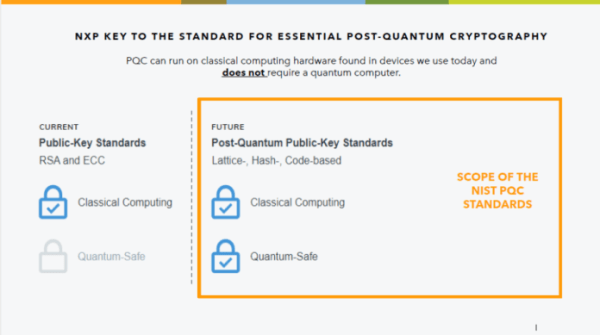
The scope of the NIST PQC standard. Click to enlarge image. (Source: NXP Semiconductors)
NIST received 69 applications from around the world for the new security standard, going through several rounds of finalists. These encryption algorithms perform two main functions: general encryption to protect information shared over public networks, and digital signatures for identification.
The new PQC algorithms will be used to develop a new public-key encryption standard that can be used in both traditional and quantum computers, allowing companies to migrate to new, secure systems ahead of the quantum threat. The draft standards are expected to be released in 2024.
The new key exchange standard will join today's standards, including NIST SP 800-56A Rev. 3, which defines the Diffie-Hellman key exchange or elliptic curve key exchange variant during the transition phase. The industry expects that at some point the two current methods will no longer be secure, and all industry products will have to migrate to the new post-quantum secure key exchange standard.
Why a new standard is needed
Cybersecurity experts believe that large-scale quantum computers, when implemented, will be able to crack modern public-key encryption systems "in a fraction of the time," leaving data, digital signatures and devices vulnerable, NXP reported.

(Source: NXP Semiconductors)
Quantum computers provide many times faster computation and "open up a whole new realm of computing" with applications in many areas, including healthcare, materials, sustainable development, financial trading and big data, as well as other complex problems and simulations , said Joppe Bos, senior chief cryptographer at NXP.
"There are not only opportunities, but also certain risks associated with the growth of quantum computing power," he said.
If there was a large-scale quantum computer with enough qubits, which we don't currently have, it would be possible to break all public-key cryptography currently in use — RSA and Elliptic Curve Cryptography (ECC) — in an instant, Bos said. He added that this has all sorts of implications for data stored today, as it could be retroactively decrypted in the future.
Some examples given where data could be compromised include over-the-air updates in security vehicles. implications, financial transactions, audit logs, and blockchain and cryptocurrency transactions. "All these applications, which are heavily based on public-key cryptography as we know it today, will become insecure," he added.
This problem was recognized at an early stage, and it was decided to look for a new public key standard that is protected not only from attacks from classical computers, but also from attacks using quantum computers, leading to post-quantum cryptography, Bos said. .
He clearly explains that post-quantum cryptography does not require a quantum computer to run the algorithms. They can run on traditional hardware platforms and CPUs. This term refers to security in the post-quantum era, also known as quantum-safe.
With NIST's announcement, companies will begin preparing their product plans for new future standards, Bos said. NXP is in a very specific market, focused on implementing high reliability, and "we need to find all these countermeasures for these new types of algorithms, which is non-trivial..." to ensure that all products - software and hardware - are secure. against advanced attacks.
"And we need to ensure that future products, and more importantly, products introduced now, can seamlessly upgrade to post-quantum cryptography using this new public key standard in the future," he said.
He refers to it. to this as "cryptographic flexibility", where there is a defined way to smoothly transform or update your crypto library so that data is secure in a post-quantum world.
"We need to make sure these new algorithms are implemented securely and can work on our existing and new platforms, so we're very busy with that right now," Bos said.
"The big advantage is that it is immune to quantum computers, but it has significant disadvantages compared to the algorithms that work now," he said.
Keys are much larger and typically slower, requiring more memory to run, he added.
So how do you prepare OEM customers for the new standard? This is mainly about setting requirements, Bos said, and helping with impact assessments.
Although the new algorithms can work on modern computers, it may not be possible on some platforms. Especially for resource-constrained platforms like smart cards, it simply won't do, Bos said, adding that they can't meet the performance requirements to run much larger and slower algorithms.
That's one of the reasons why NXP began developing new hardware designs last year to ensure that the company can accelerate the post-quantum cipher for future products.
But it's a huge challenge for all industries, from mobile to the industrial Internet of Things, Bos said. Every segment that uses some form of security will need to upgrade to this new standard in the coming decades.
Initially, many governments are rolling out roadmaps with a migration period that requires compliance with both post-quantum cryptography and current crypto standards "to be secure," Bos said. "When there is enough trust in this new post-quantum cryptographic standard, we will abandon RSA and ECC entirely."
Learn more about NXP Semiconductors
Source: electronicproducts.com